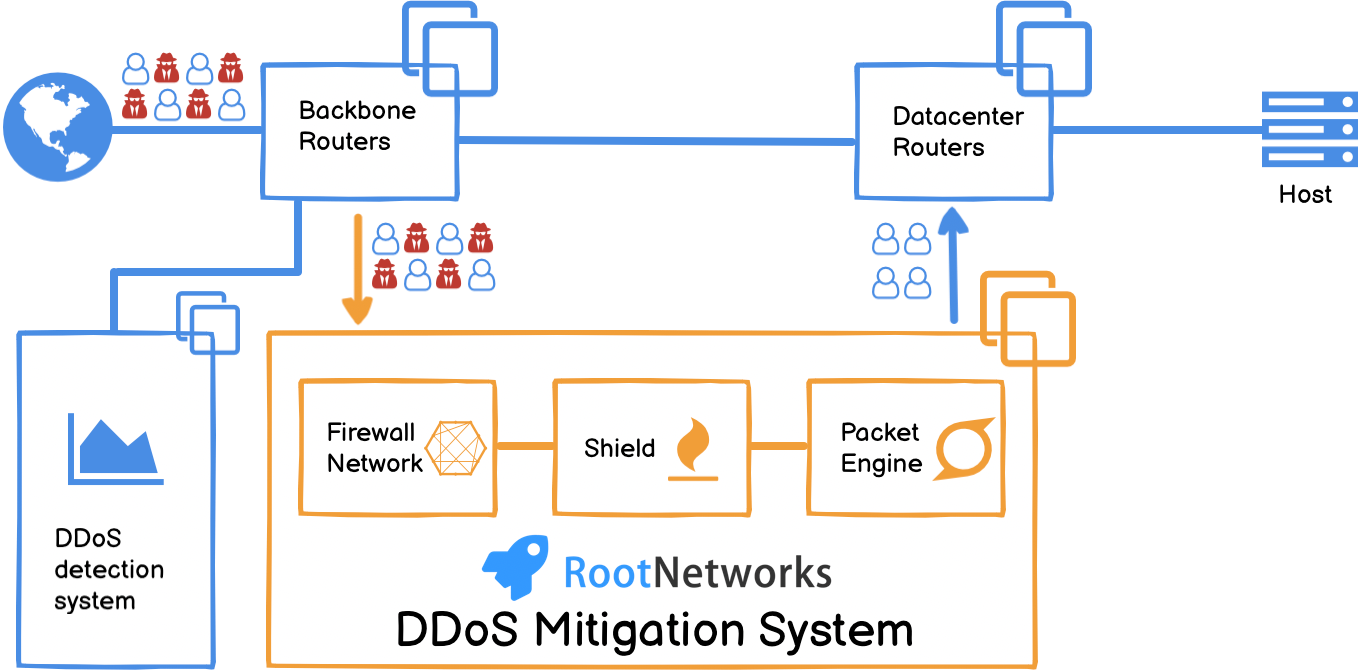
Our high-performance firewall built on Tilera is different from most providers. Our super powerful packet processing engine, it can 100% process small and large packets in real-time to provide ultra-low latency mitigation. Our DDoS protection cloud provides high-performance layer 3, 4, and 7 DDoS protection with full control and clear insight.